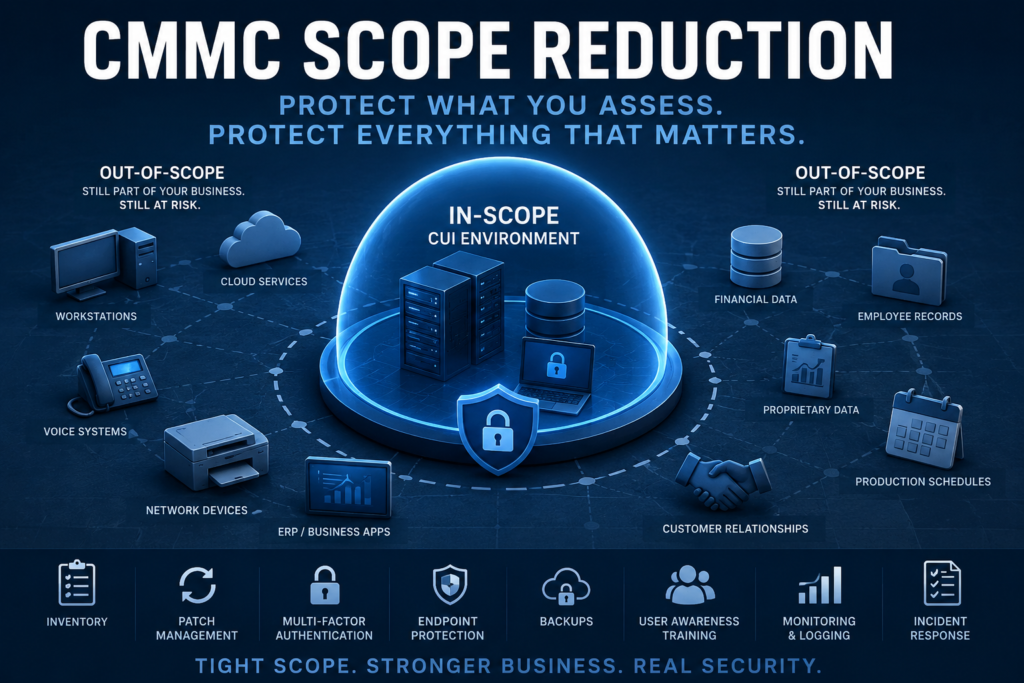
If you have spent any time researching CMMC, you have heard the advice: narrow your scope. Get assets out of scope wherever you can. Segment your CUI environment. Reduce your assessment boundary.
That advice is correct. I agree with it 100 percent. A tightly scoped enclave is easier to assess, easier to maintain, and almost always less expensive to certify. If you are working toward Level 2, scope reduction should be one of the first strategic conversations you have, ideally before you spend a dollar on tooling or remediation.
But there is a second conversation that needs to happen alongside the first one, and it gets far less attention.
Out of Scope Is Not Out of Danger
Getting an asset out of scope for CMMC does not get it out of scope for cybersecurity. Your out-of-scope workstations, servers, network gear, and cloud tenants are still part of your business. They still hold proprietary information, financial data, employee records, customer relationships, quoting and estimating data, production schedules, and operational knowledge that matters. They still sit on networks adjacent to your CUI enclave. They are still targets.
The threat actors who were never going to limit themselves to your assessment boundary do not care which assets you marked as out of scope on your asset inventory. They care about what they can encrypt, exfiltrate, or extort.
A contractor who passes a CMMC assessment with a beautifully minimized scope and then gets ransomware through their out-of-scope ERP system has not actually solved their security problem. They have solved their compliance problem. Those are not the same thing, and conflating them is one of the most expensive mistakes a small or mid-sized defense contractor can make.
The CMMC Program Already Acknowledges This
The CMMC scoping guidance for Level 2 includes a category called Contractor Risk Managed Assets, or CRMA. These are assets that are not intended to process, store, or transmit CUI but that could, due to their position in the network or their relationship to in-scope systems. The program does not require these assets to meet the full weight of NIST SP 800-171, but it does require contractors to manage the risk they present, document them in the asset inventory, and address them in the System Security Plan.
In other words, the framework itself is telling you that out-of-scope is not a binary. There is a middle category of assets that demand attention even when they are not directly assessed. And beyond CRMA, there is everything else: the truly out-of-scope side of your business that still needs to function, still needs to be defended, and still represents real exposure if it goes down.
What Hygiene Looks Like for Out-of-Scope Assets
When you build your scope reduction strategy, build a parallel strategy for the assets you are pulling out. None of this needs to meet the full rigor of a CMMC assessment, but it absolutely needs to exist as a real program with a real owner.
Asset inventory. You cannot protect what you do not know about. Maintain a current list of every device, server, application, and cloud service in the out-of-scope environment, including who owns it and what data it touches. This is also the foundation for everything else on this list.
Patch management. Operating systems, firmware, and third-party applications need to be updated on a defined cadence. Most successful intrusions exploit vulnerabilities that have had patches available for months or years.
Multi-factor authentication. Apply MFA to every account that supports it, especially email, remote access, administrative accounts, and anything internet-facing. This single control blocks the majority of credential-based attacks.
Endpoint protection. Modern endpoint detection and response, or at minimum a reputable managed antivirus product, on every workstation and server. The cost has come down to the point where there is no defensible reason to skip this.
Backups. Regular, tested, and ideally immutable. If your only backup strategy is the one your ERP vendor mentioned in passing during onboarding, you do not have a backup strategy. Test restores quarterly.
User awareness training. Phishing remains the most common initial access vector. A short monthly training cadence with simulated phishing produces measurable results and costs very little.
Basic monitoring and logging. You do not need a full SIEM for out-of-scope assets, but you do need enough visibility to know when something is wrong. Centralized log collection, alerting on key events, and someone who actually looks at the alerts.
Documented incident response. A simple, written plan that says who does what when something goes wrong. Practice it once a year. The first time you read your incident response plan should not be during an actual incident.
Two Strategies, One Business
Scope reduction is a CMMC strategy. Cybersecurity hygiene is a business strategy. You need both, and they need to be designed together rather than in sequence.
The contractors who get this right end up with a tightly scoped CUI enclave that passes assessment efficiently, sitting inside a broader environment that is also defensible. The contractors who get it wrong end up with a clean assessment report and a business that is one phishing email away from a very bad week.
If you are working through scope decisions right now and want a second set of eyes on how the in-scope and out-of-scope sides of your environment fit together, that is exactly the kind of work we do at PhasedLogix. Reach out and we can talk through it.

